- California Assembly OKs highest minimum wage in nation
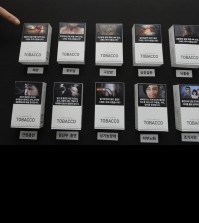
- S. Korea unveils first graphic cigarette warnings
- US joins with South Korea, Japan in bid to deter North Korea
- LPGA golfer Chun In-gee finally back in action
- S. Korea won’t be top seed in final World Cup qualification round
- US men’s soccer misses 2nd straight Olympics
- US back on track in qualifying with 4-0 win over Guatemala
- High-intensity workout injuries spawn cottage industry
- CDC expands range of Zika mosquitoes into parts of Northeast
- Who knew? ‘The Walking Dead’ is helping families connect
S. Korean spy agency sought to hack into KakaoTalk: leaked data
By Kang Yoon-seung
SEOUL, July 13 (Yonhap) — South Korea’s spy agency made inquiries to a foreign hacking firm last year to seek ways to penetrate the country’s most-popular mobile messenger KakaoTalk, leaked data suggested Monday.
The suspicion came as the whistleblowing website WikiLeaks revealed “1 million searchable e-mails” through its platform that included those exchanged by Italian surveillance malware vendor Hacking Team and an unidentified South Korean entity.
South Korea’s National Intelligence Service refused to comment on the suspicion, but sources said that the unidentified entity dubbed “the 5163 Army Unit” is highly likely to refer to the spy agency.
“They also asked about the progress of Kakao Talk which they mentioned is very commonly used in their country,” one of the leaked documents from Hacking Team showed. The e-mails were exchanged in March 2014.
KakaoTalk, South Korea’s most popular free mobile messenger, has 35 million local users in the country with a population of 50 million.
“We discussed about the issues SKA raised in their ticket, mainly on their concerns about the recent exposure especially when the local news are also highlighting the possibility that the government is using RCS to monitor their own citizens,” Hacking Team also said.
SKA stands for South Korea Army, while RCS refers to Remote Control System technology.
The RCS technology can be used to hack data by installing spyware, allowing hackers to manipulate and track smartphones and computers.
Another email read “I’ve already informed our R&D team of KakaoTalk. In general, we are getting solid results from exploit developers, hopefully we will be able to provide some remote exploits for Android and other platforms in the near future.”
The data also insisted the 5163 Army Division spent 686,410 euros (US$763,013) since 2012 on RCS programs.
Daum Kakao, the messenger’s operator, said its server has never been attacked, adding users are currently safe from any penetration.
“We cannot give comments on only assumptions,” a Daum Kakao official said. “However, we can say that our servers were never attacked.”
“Hackers may, however, intrude the operating systems or device. We ask users to take basic precautionary measures to keep their phones safe,” the official added.











![일본 사도광산 [서경덕 교수 제공. 재판매 및 DB 금지]](http://www.koreatimesus.com/wp-content/uploads/2024/07/PYH2024072610800050400_P4-copy-120x134.jpg)


